Firmware Under Siege: Protecting Your Devices at the Lowest Level
Dive into firmware security, exploring reverse engineering, critical vulnerabilities like LogoFAIL, and advanced secure update mechanisms essential for protecting modern devices.
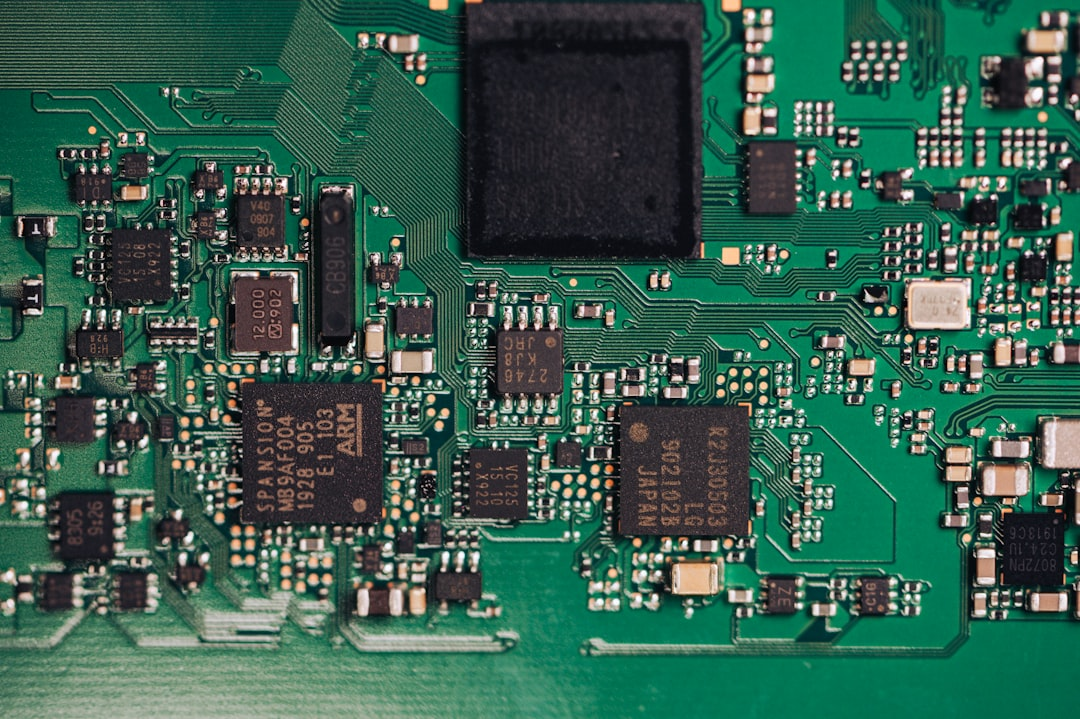
Ever wondered what truly powers your computer, phone, or even that smart toaster before the operating system even loads? It’s firmware – the silent, foundational code that orchestrates a device’s hardware. But what happens when this bedrock of technology becomes a target? 🔐
In today’s interconnected world, firmware security isn’t just a niche concern for hardware geeks; it’s a front-line battleground for cyber defense. From IoT devices flooding our homes to critical infrastructure, compromised firmware can grant attackers unparalleled persistence and control, often below the visibility of traditional security tools. This post will delve into the critical realm of firmware security, exploring the dark art of reverse engineering, the discovery of insidious vulnerabilities, and the indispensable mechanisms designed to keep our digital foundations safe.
The Invisible Battleground: Why Firmware Security Matters NOW
Imagine a gatekeeper who holds the master keys to your entire digital kingdom, but operates entirely out of sight. That’s firmware. It’s the essential software embedded directly into hardware devices, enabling them to boot up, communicate with components, and perform their basic functions. Unlike application software, firmware is notoriously difficult to inspect, update, or secure, making it a prime target for sophisticated adversaries.
The stakes have never been higher. Recent trends, highlighted by reports from organizations like CISA and major cybersecurity firms throughout 2024-2025, show a clear uptick in attacks targeting the firmware layer. Why? Because a compromise here grants attackers unparalleled privilege, persistence, and the ability to evade detection for extended periods. Think supply chain attacks that inject malicious code before a device even leaves the factory, or sophisticated rootkits that survive operating system reinstalls. Protecting this lowest level is paramount to maintaining digital trust.
Unmasking the Core: Firmware Reverse Engineering
To secure firmware, one must first understand it. This is where firmware reverse engineering comes in – a specialized discipline that involves dissecting compiled firmware binaries to understand their functionality, identify vulnerabilities, or even extract proprietary information. It’s a bit like taking apart a complex machine piece by piece to see how it works, but with code.
Did You Know? Most firmware is proprietary and distributed as compiled binaries, meaning the original source code is not available. Reverse engineering aims to recreate a human-readable understanding from these binaries.
Security researchers, malware analysts, and even nation-state actors employ various tools and techniques for this purpose.
Extraction: Often, firmware is embedded within flash memory chips or distributed in proprietary archive formats. Tools like
Binwalkare indispensable here, capable of identifying and extracting various file systems, compression schemes, and embedded binaries from firmware images.1 2
# Extract components from a firmware image binwalk -eM firmware.bin
- Disassembly & Decompilation: Once extracted, the binaries are fed into powerful reverse engineering suites.
- IDA Pro and Ghidra (the NSA’s open-source tool) are industry standards. They disassemble machine code into assembly language and attempt to decompile it into higher-level pseudo-code (like C), making it much easier to analyze.
- Analysts look for critical functions, communication protocols, cryptographic routines, and potential entry points for exploitation.
- Emulation & Dynamic Analysis: Static analysis (examining code without running it) has its limits. Tools like QEMU can emulate various hardware architectures, allowing researchers to run and debug firmware images in a controlled environment. This helps in understanding runtime behavior, state transitions, and triggering hidden code paths.
This meticulous process allows researchers to identify weaknesses, whether they are hardcoded credentials, buffer overflows, or logical flaws that an attacker could exploit to gain control.
Deep-Seated Dangers: Firmware Vulnerabilities & Real-World Exploits
The consequences of firmware vulnerabilities are severe, often leading to full system compromise, data exfiltration, or even bricking devices. The unique position of firmware at the root of trust makes it an attractive target.
Common firmware vulnerabilities include:
- Insecure Bootloaders: Lack of cryptographic signature verification allows malicious firmware to be loaded.
- Hardcoded Credentials: Default passwords or API keys easily extracted and abused.
- Buffer Overflows/Underflows: Classic memory corruption flaws leading to arbitrary code execution.
- Improper Input Validation: Allowing attackers to inject malicious data into firmware functions.
- Weak Cryptography: Using outdated algorithms or improperly implemented encryption.
- Insecure Update Mechanisms: The very process meant to secure firmware can be a weak link if not properly designed.
“A single vulnerability in the firmware layer can unravel an entire chain of security measures, demonstrating its critical role as the foundation of trust.”
Real-World Examples:
1. LogoFAIL (2023-2024): A critical vulnerability impacting the UEFI (Unified Extensible Firmware Interface) firmware across hundreds of millions of devices from major vendors like Lenovo, Acer, Dell, HP, and Intel. This flaw allowed attackers to inject malicious images into the boot process, hijacking the execution flow before the operating system even starts. By manipulating logo files, attackers could achieve persistent, stealthy malware execution. This was a particularly insidious attack as it bypassed Secure Boot protections.
2. BlackLotus (2023): An infamous UEFI bootkit that exploited a known Secure Boot bypass vulnerability (CVE-2022-21894). BlackLotus allowed threat actors to gain control over the boot process, disable security features, and deploy persistent malware, effectively taking over the system before the OS could load any defenses.
3. Supply Chain Attacks: While SolarWinds was a software supply chain attack, the concept extends to firmware. Malicious modifications during manufacturing or distribution can embed backdoors directly into hardware firmware, making detection incredibly difficult. Researchers have consistently warned that attackers are increasingly targeting manufacturers and suppliers to compromise devices at scale.
Critical Warning: Firmware attacks like LogoFAIL and BlackLotus demonstrate that even foundational security mechanisms like Secure Boot are not impenetrable if the underlying firmware logic is flawed. Regular patching and diligence are non-negotiable.
Fortifying the Foundation: Secure Firmware Update Mechanisms
Given the severe impact of firmware vulnerabilities, robust, secure update mechanisms are paramount. These systems ensure that only authorized, verified firmware can be installed, patching vulnerabilities and adding new features without introducing new risks.
Cryptographic Signing: This is the cornerstone of secure updates. Every firmware image must be cryptographically signed by the device manufacturer using a private key. The device’s firmware, in turn, contains the corresponding public key to verify the signature. If the signature doesn’t match or is tampered with, the update is rejected.
1 2 3 4 5 6
# Pseudocode for Firmware Update Verification function verifyFirmwareUpdate(firmwareImage, signature, publicKey): if calculateHash(firmwareImage) == decrypt(signature, publicKey): return true // Signature valid, firmware is authentic else: return false // Signature invalid, reject updateSecure Boot: An industry-wide standard (especially prevalent in UEFI systems), Secure Boot ensures that only trusted code (signed by a trusted authority) can be loaded during the boot process. It validates each stage of the boot chain, from the firmware itself to the bootloader and eventually the operating system kernel.
Rollback Protection: A crucial defense against downgrade attacks. If an attacker manages to force an older, vulnerable version of firmware onto a device, rollback protection mechanisms (often using monotonic counters or anti-replay mechanisms) prevent it from booting, ensuring that only current, patched firmware can run.
Over-the-Air (OTA) Updates: For IoT and embedded devices, manual updates are impractical. OTA updates allow firmware to be securely delivered and installed remotely. This requires robust transport security (e.g., TLS/SSL) and often uses delta updates to minimize bandwidth.
Remote Attestation: More advanced systems use remote attestation to verify the integrity of a device’s firmware and software stack at runtime. A trusted entity can challenge a device, which then provides cryptographic proof (often leveraging a Trusted Platform Module - TPM) of its boot state and firmware versions. This helps detect persistent infections.
| Security Mechanism | Primary Goal | Key Benefit | Real-World Impact |
|---|---|---|---|
| Cryptographic Signing | Authenticity & Integrity of Firmware | Prevents installation of unauthorized/modified images | Blocks supply chain injection and tampered updates |
| Secure Boot | Ensure only trusted code boots | Establishes a hardware-backed root of trust | Prevents bootkits and malicious OS loaders (e.g., BlackLotus mitigation) |
| Rollback Protection | Prevent downgrades to vulnerable versions | Defends against known exploit re-use | Ensures devices run the latest security patches |
| Remote Attestation | Verify runtime integrity of firmware/software | Detects post-boot compromise and persistent malware | Crucial for Zero Trust architectures and compliance in critical environments |
Beyond the Basics: Emerging Trends & Best Practices
The landscape of firmware security is constantly evolving. Staying ahead requires embracing new technologies and adopting a proactive posture.
- Platform Firmware Resiliency (PFR) - NIST SP 800-193: This standard emphasizes the importance of hardware-rooted trust, detection of firmware corruption, and automated recovery mechanisms. Devices designed with PFR can protect, detect, and recover firmware from attacks, even if compromised during manufacturing.
- Software Bill of Materials (SBOM) for Firmware: Just as critical for software, an SBOM for firmware provides transparency into all components, libraries, and open-source elements within a firmware image. This helps identify known vulnerabilities (like Log4Shell-type issues in embedded components) and manage supply chain risks more effectively.
- AI/ML in Vulnerability Detection: Researchers are increasingly using AI and machine learning to analyze vast amounts of firmware code, identify patterns of vulnerabilities, and even predict potential exploits, accelerating the discovery of flaws that manual analysis might miss.
- Post-Quantum Cryptography (PQC): With the advent of quantum computing, current asymmetric cryptography (like RSA and ECC used in firmware signing) will eventually be breakable. The industry is actively researching and standardizing PQC algorithms to ensure the long-term security of firmware updates. Manufacturers are beginning to integrate PQC readiness into their product roadmaps.
Key Takeaways
- Firmware is the foundation: It’s the critical layer underpinning all device security, and attacks here grant deep, persistent access.
- Reverse engineering is a double-edged sword: Essential for researchers to find vulnerabilities, but also a tool for attackers.
- Vulnerabilities are real and impactful: Recent exploits like LogoFAIL demonstrate the severe risks of flawed firmware and even bypass foundational protections.
- Secure update mechanisms are non-negotiable: Cryptographic signing, Secure Boot, and rollback protection are vital defenses against compromise.
- Proactive security is key: Embracing PFR, SBOMs, and preparing for post-quantum cryptography are crucial for future-proofing devices.
Conclusion
Firmware security is no longer an afterthought; it is the ultimate frontier in cybersecurity. As our world becomes increasingly saturated with smart, connected devices, the integrity of the code at their lowest level will dictate our collective digital safety. By understanding the intricacies of firmware reverse engineering, recognizing common vulnerabilities, and rigorously implementing secure update mechanisms, we can collectively build a more resilient digital ecosystem. Are you ready to secure your foundation? 🛡️
—Mr. Xploit 🛡️