TryHackMe Labs Series: A Daily Hands-On Cybersecurity Journey
The Beginning of a New Adventure
Picture this: It’s late at night, the glow of multiple terminals illuminating your face, your fingers dancing across the keyboard as you finally crack that elusive vulnerability you’ve been hunting for hours. That rush of adrenaline, that moment of triumph—this is what cybersecurity feels like when you truly understand it.
But here’s the truth that nobody tells beginners: you don’t get there by reading textbooks alone.
The path to cybersecurity mastery is paved with broken shells, failed exploits, and countless hours of hands-on practice. After years of navigating this journey myself, I’ve decided to create something I wish I had when I started—a structured, daily learning companion that takes you from absolute beginner to confident practitioner.
Welcome to the TryHackMe Lab Series. And yes, we’re starting on January 1st, 2026.
Every expert was once a beginner. The difference? They never stopped practicing.
Meet Your Guide: Mr. Xploit
Before we dive in, let me introduce myself. I’m Ayush Kumar Jha, but in the cybersecurity world, you can call me Mr. Xploit—a name I earned through countless late nights breaking (and securing) systems in controlled environments.
As a Cyber Security student, my journey has been anything but linear. I’ve fumbled through my first Nmap scan, accidentally locked myself out of my own virtual machines, and yes—I’ve even crashed a lab environment or two. These “failures” weren’t setbacks; they were lessons that books could never teach.
What Drives Me
My toolkit spans across multiple domains:
| Domain | Focus Areas |
|---|---|
| 🌐 Network Security | Packet analysis, firewall bypass, network mapping |
| �️ Web Security | OWASP Top 10, injection attacks, authentication flaws |
| � Penetration Testing | Reconnaissance, exploitation, post-exploitation |
| 🛡️ Ethical Hacking | Responsible disclosure, legal boundaries |
| 📚 Security Fundamentals | CIA triad, threat modeling, risk assessment |
No amount of theory can replace the feeling of successfully exploiting your first vulnerability—then immediately understanding how to patch it.
This blog series is my way of giving back. Every stumble, every breakthrough, every “aha!” moment I’ve experienced—I’m packaging it all into digestible, daily lessons that will transform how you approach cybersecurity.
Why This Series Will Change Everything
Let me be honest: cybersecurity education is broken.
Too many courses promise mastery but deliver only theory. Too many tutorials show you what to type without explaining why. And too many learners give up, not because they lack ability, but because they lack a structured path forward.
The TryHackMe Lab Series addresses every one of these problems.
The Promise I’m Making to You
Every single day, starting January 1st, 2026, I will publish a complete walkthrough of one TryHackMe lab. But these won’t be your typical “copy-paste the commands” tutorials.
Each post will answer three critical questions:
- What are we doing? (The technical execution)
- Why does it work? (The underlying principles)
- How do defenders stop this? (The security mindset)
This series is designed for the curious—those who aren’t satisfied with answers like “just run this command.” If you want to understand the why behind every exploit, you’re in the right place.
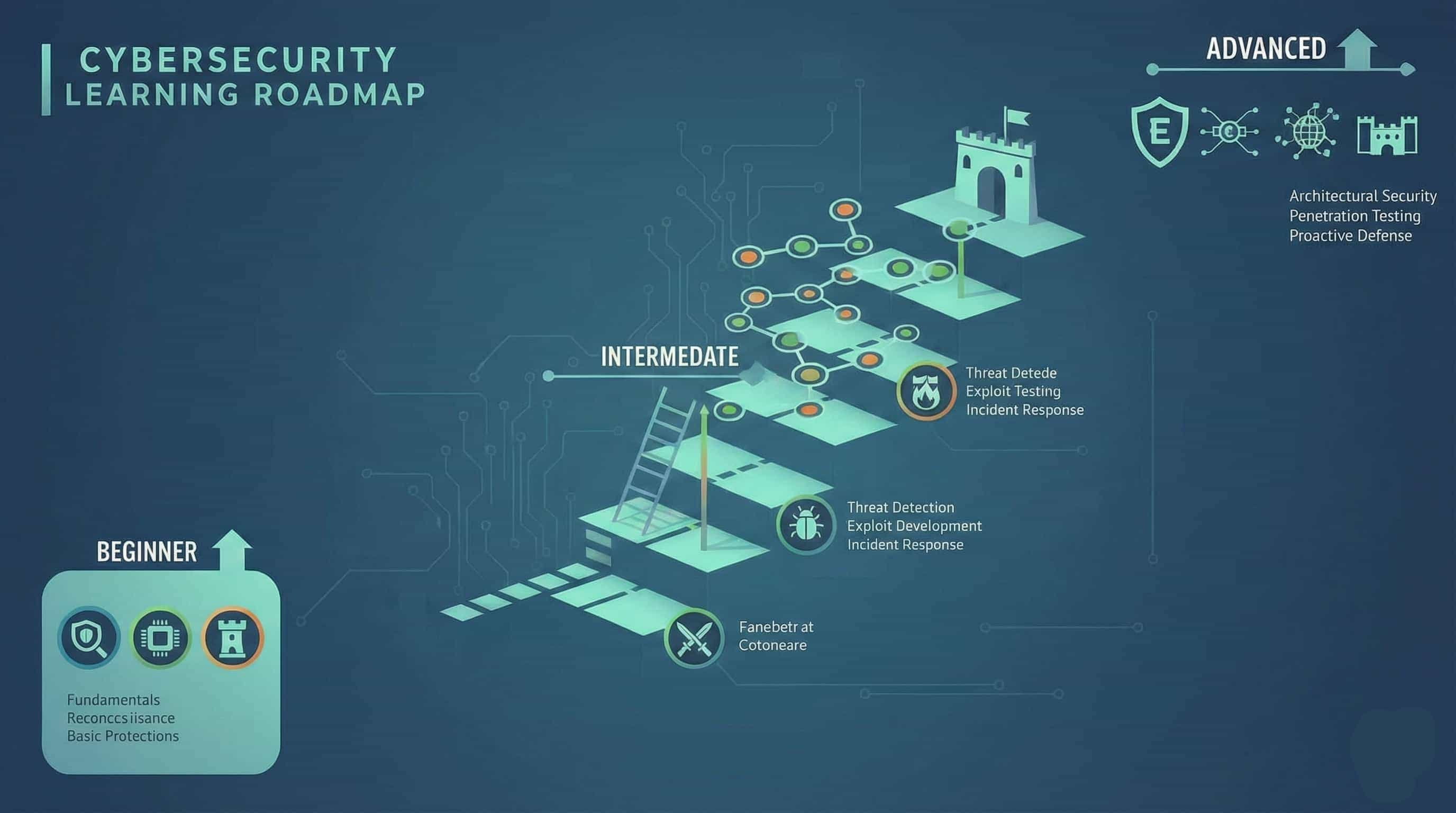
The Roadmap: Your Journey from Zero to Hero
I’ve meticulously organized the labs into a progressive learning path. You won’t be thrown into the deep end on Day 1—instead, we’ll build your skills layer by layer, ensuring you have a rock-solid foundation before tackling advanced challenges.
🟢 Phase 1: Building Your Foundation
Duration: Weeks 1-4
Difficulty: Beginner
The journey begins with fundamentals. I know, I know—you want to jump straight into hacking. But trust me on this one: the hackers who skip fundamentals are the ones who plateau early.
In this phase, we’ll master:
- Linux Command Line — Because 90% of security tools run on Linux
- Networking Essentials — TCP/IP, DNS, HTTP—the language systems speak
- Web Fundamentals — How browsers and servers communicate
- Security Principles — Thinking like both attacker and defender
Don’t skip the fundamentals. The difference between a script kiddie and a real security professional lies in understanding the “why” behind every command.
🟡 Phase 2: Technical Skill Building
Duration: Weeks 5-10
Difficulty: Intermediate
With foundations in place, we enter the realm of practical reconnaissance and analysis. This is where things start getting exciting.
What You’ll Learn:
| Skill Area | Tools & Techniques |
|---|---|
| System Enumeration | Nmap, Netcat, manual techniques |
| Web Vulnerabilities | Burp Suite, browser DevTools |
| Authentication Attacks | Credential testing, session analysis |
| Information Gathering | OSINT, directory enumeration |
By the end of this phase, you’ll be able to look at any system and instinctively identify its potential weaknesses.
🟠 Phase 3: Offensive Security
Duration: Weeks 11-18
Difficulty: Intermediate to Advanced
Now we enter attack mode.
This is the phase most people think of when they imagine “hacking”—exploiting vulnerabilities to gain unauthorized access. But remember: we do this ethically, in controlled environments, to understand how attackers think so we can better defend against them.
Core Topics:
- 💉 Injection Attacks — SQL injection, command injection, LDAP injection
- 📁 File Inclusion — LFI/RFI and what they reveal
- 🔓 Privilege Escalation — Going from low-privilege user to root/admin
- ⚔️ Exploitation Frameworks — Metasploit and manual exploitation
Always remember: the goal isn’t just to “pwn the box.” It’s to understand the vulnerability so deeply that you could write the patch yourself.
🔵 Phase 4: Defensive Security
Duration: Weeks 19-24
Difficulty: Advanced
Attack is only half the equation. In this phase, we flip the script and become defenders.
Understanding defense is what separates hobbyist hackers from security professionals. Every company needs people who can detect attacks, respond to incidents, and harden systems before threats arrive.
Defense Arsenal:
- 📊 Log Analysis — Finding needles in haystacks of data
- 🚨 Incident Response — What to do when things go wrong
- 🦠 Malware Analysis — Understanding hostile code
- 🏰 Network Defense — Firewalls, IDS/IPS, segmentation
🔴 Phase 5: Advanced Operations
Duration: Week 25+
Difficulty: Expert
The final frontier. By this point, you’ll have the skills to tackle real-world scenarios that mirror what professional red and blue teams face daily.
Advanced Topics:
- 🏢 Active Directory Attacks & Defense — The backbone of enterprise security
- 🔴🔵 Red Team vs. Blue Team Exercises — Full-spectrum operations
- 🎯 Advanced Exploitation — Custom exploits and evasion techniques
- 🏆 Capstone Challenges — Putting it all together
What Each Lab Walkthrough Includes
Consistency breeds mastery. Every single post in this series follows a proven structure designed for maximum learning:
| Section | What You’ll Find |
|---|---|
| 🎯 Lab Overview | Objectives, difficulty rating, skills you’ll develop |
| 🔧 Prerequisites | Required tools, setup instructions, assumed knowledge |
| 📝 Step-by-Step Walkthrough | Detailed commands with explanations and screenshots |
| 💡 Key Concepts | The theory behind what we just did |
| ⚠️ Common Mistakes | Pitfalls I’ve seen (and made) so you don’t have to |
| 🌍 Real-World Applications | How this applies to actual security work |
 Interactive, hands-on learning with TryHackMe’s real-world simulation environments
Interactive, hands-on learning with TryHackMe’s real-world simulation environments
The Ethical Boundary
Let me be absolutely clear about something:
Everything in this series is performed in authorized TryHackMe environments exclusively for educational purposes. Attempting these techniques on systems you don’t own or have explicit permission to test is illegal, unethical, and will end your career before it starts.
This isn’t just a disclaimer—it’s a core principle. Ethical hackers are defined by their restraint, not their capability. The skills you’ll learn here are powerful, and with great power comes great responsibility.
The law is clear:
- ❌ Unauthorized access = criminal offense
- ❌ Testing without permission = career suicide
- ❌ Sharing exploits irresponsibly = enabling criminals
The professional path:
- ✅ Bug bounties on authorized programs
- ✅ Penetration testing with signed contracts
- ✅ Red team operations with explicit scope
- ✅ CTF competitions and controlled labs
Your Investment, Your Reward
Starting January 1st, 2026, you’ll receive a new lab walkthrough every single day. That’s 365 opportunities to grow, to learn, and to transform yourself from a curious beginner into a confident cybersecurity practitioner.
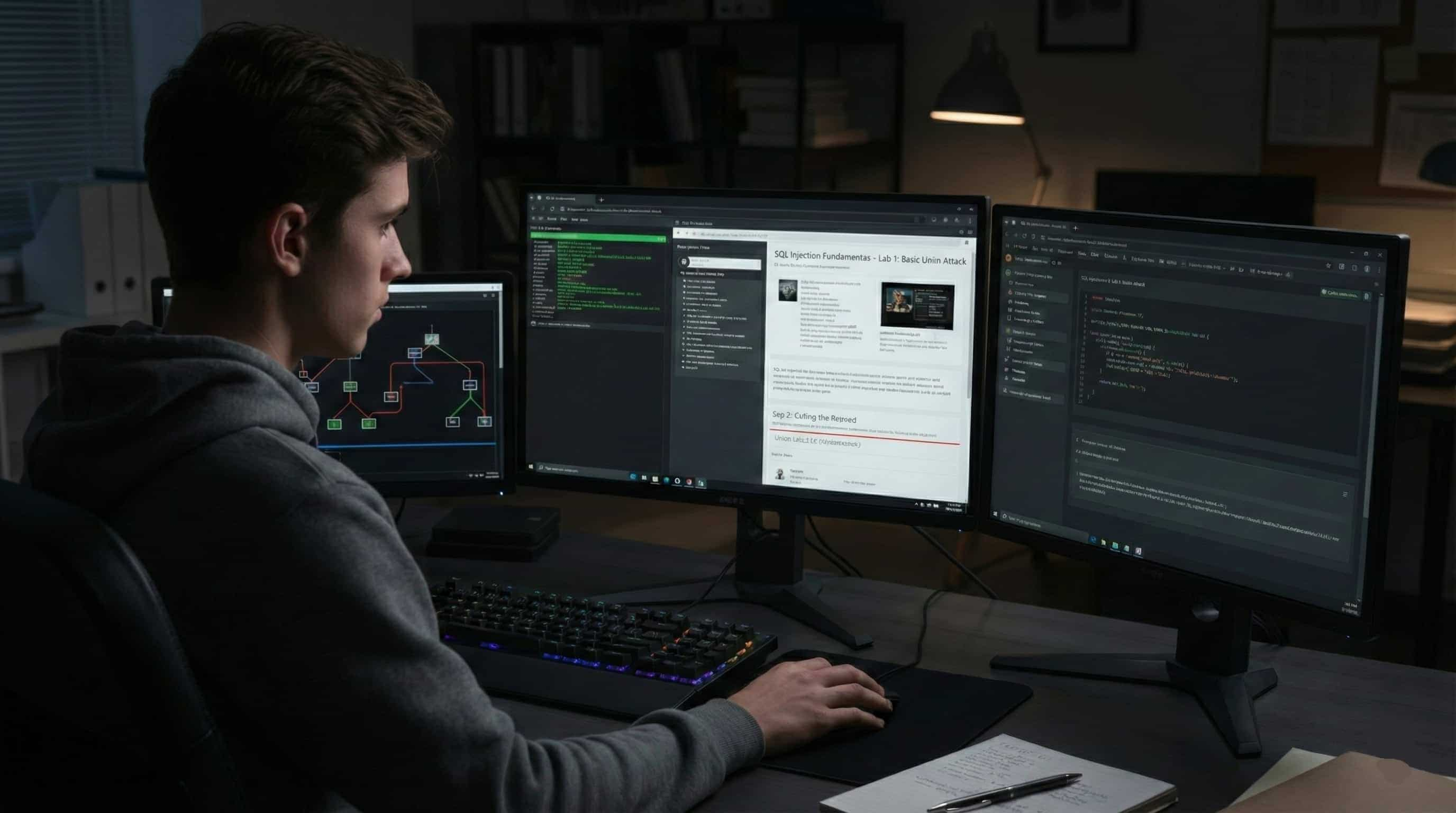
 The focused dedication that transforms curious learners into skilled professionals
The focused dedication that transforms curious learners into skilled professionals
What This Series Will Give You
By following along consistently, you’ll develop:
- 🧠 Deep Understanding — Not just how to run tools, but how systems actually work
- �️ Practical Skills — Battle-tested techniques you can apply immediately
- � Career Readiness — Portfolio-building experiences that employers value
- 🏆 CTF Confidence — The problem-solving mindset that wins competitions
Whether your goal is to ace CTF competitions, land your first security job, transition into ethical hacking, or simply understand how attackers think—this series will guide you every step of the way.
The Call to Action
The path from beginner to cybersecurity professional is challenging. There will be frustrating nights, confusing concepts, and moments where you want to give up. But I promise you this: if you stick with this series, you will transform.
Learn. Break. Secure. Repeat.
Mark your calendar for January 1st, 2026. Subscribe, bookmark, do whatever you need to do—because when that first lab walkthrough drops, your journey begins.
The cybersecurity community is waiting for you. The question is: are you ready?
See you on Day One.
—Mr. Xploit 🛡️
Have questions about the series? Want to suggest specific labs or topics? Found this post helpful? Drop a comment below or reach out on social media. The best journeys are the ones we take together.
