Secure API Design Building Resilient Interfaces for the Digital Age
Master secure API design with robust input validation, intelligent rate limiting, and modern authentication patterns to protect your digital interfaces.
Master secure API design with robust input validation, intelligent rate limiting, and modern authentication patterns to protect your digital interfaces.

Discover how the financial sector combats evolving cyber threats, from PCI DSS v4.0 to SWIFT security and the dark side of insider trading through hacking.

Discover how Remote Browser Isolation (RBI) is critical for zero trust architectures, containing web-based threats, and enhancing cybersecurity in a rapidly evolving digital landscape.

Build a robust cybersecurity incident response plan using tabletop exercises and NIST's six phases. Learn to prepare, detect, contain, eradicate, recover, and learn from cyber threats effectively.

Learn to master third-party risk management with advanced vendor security assessments, continuous monitoring, and robust SLA requirements in today's AI-driven threat landscape.

Discover why robust encryption key management, including HSMs, key rotation, and avoiding sprawl, is critical for modern data security.

Discover how Vulnerability Disclosure Programs create a safe legal haven for security researchers, fostering collaboration and strengthening cybersecurity defenses against evolving threats.
Explore how AI, especially LLMs, supercharges phishing attacks and learn advanced defenses against this new wave of sophisticated social engineering.
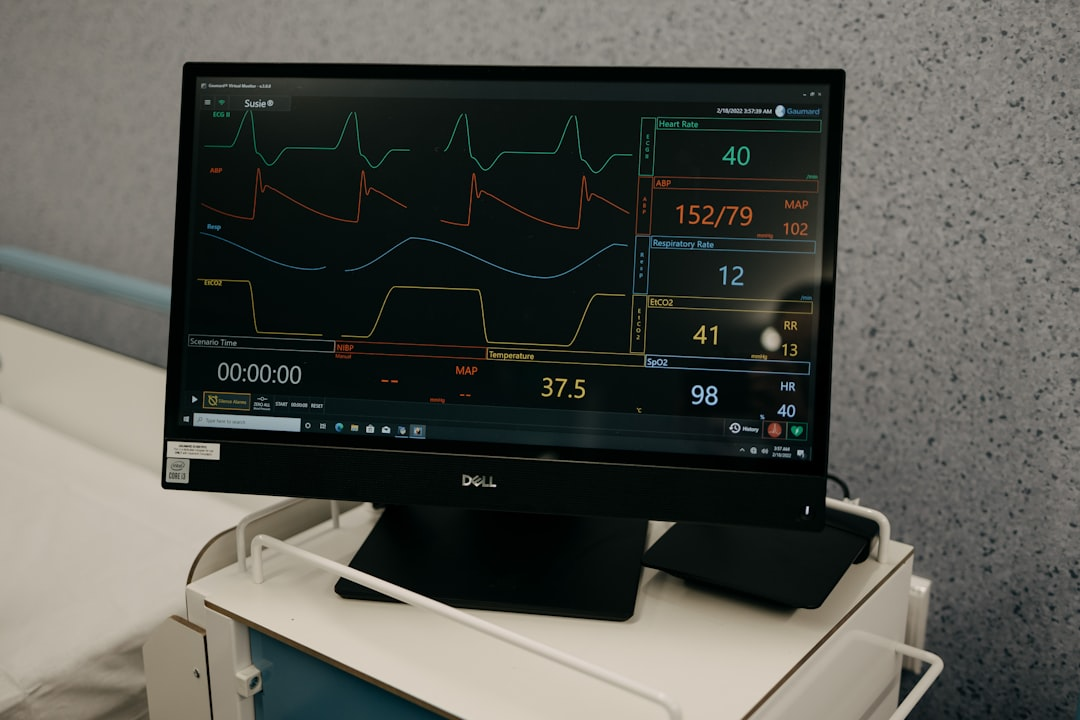
Explore the critical challenges of healthcare cybersecurity, focusing on ransomware and medical device vulnerabilities. Learn how to protect patient data and ensure HIPAA compliance in 2024 and beyond.
Master microservices security with the latest strategies. Learn how service mesh, mTLS, and API gateway controls build a robust, zero-trust defense for your distributed applications.